NDA-Proof Document Sharing: Technical Controls Beyond Legal Agreements for Marketing Firms
Firma Editorial
Document Workflow Expert
TL;DR
NDAs create legal recourse; they don't prevent sharing. NDA-proof document sharing requires technical controls that make sharing structurally difficult — view-only access (no download), time-limited links, access logs (provable if shared), and revocation capability. Together, these controls align your operational security with the protections your NDA is designed to provide.
NDA-Proof Document Sharing: Technical Controls Beyond Legal Agreements for Marketing Firms
An NDA is a legal instrument. It creates obligations and, if violated, provides legal recourse. What it doesn't do is prevent a document from being forwarded, downloaded, printed, or screenshotted.
For marketing firms sharing sensitive materials — strategy documents, competitive intelligence, proprietary frameworks, client data — the NDA is a necessary starting point, not a complete protection. The operational layer — technical controls — determines whether the NDA protection is actually functional.
The Gap Between Legal and Operational
A standard agency NDA prohibits the recipient from sharing confidential materials. In practice:
- You email a confidential document to a client contact
- The contact forwards it to a colleague without thinking about the NDA implications
- That colleague leaves for a competitor and takes the email thread with them
At no point in this chain did anyone intend to violate the NDA. The technical friction required to share the document was zero. The NDA created an obligation, but the operational setup removed any practical barrier.
Technical controls close this gap. They don't replace the legal obligation — they make the legal obligation operational.
The Four Technical Controls for NDA-Aligned Document Sharing
Control 1: View-Only Access
Deliver sensitive documents with view-only access rather than downloadable links. The recipient can read the document but not download a local copy that can be forwarded separately.
This doesn't prevent screenshotting, but it significantly raises the friction for sharing: the recipient would have to deliberately capture and re-share the content, rather than accidentally forwarding an attachment.
Most portal platforms support view-only delivery. The document opens in the browser; no download button appears.
Control 2: Time-Limited Access
Set an expiry on sensitive document links. A strategy document shared for client review might have a 30-day access window. A proposal sent to a prospect might expire if not accessed within 14 days.
Time-limited access ("time-bomb" sharing, in Firma's terminology) means the document becomes inaccessible automatically, without requiring you to manually revoke each share. This is particularly useful for:
- Competitive intelligence shared for a specific review period
- Draft strategies during a review process
- Proposals that shouldn't remain accessible indefinitely
Control 3: Access Logging
Document access logs create an audit trail: who accessed the document, when, and from what IP/device. This serves two NDA-related purposes:
Deterrence: People who know their access is logged are more careful about what they do with documents.
Evidence: If a confidential document is later found to have been shared inappropriately, the access log provides a timeline that may identify when and by whom the original access occurred.
Access logs don't prevent sharing, but they're a significant operational signal — and they're provable evidence in any dispute about how a document was handled.
Control 4: Revocation Capability
The ability to revoke access to a document at any time is the backstop for all other controls. If circumstances change — a deal falls through, a relationship ends badly, a contact leaves for a competitor — you can cut off access to sensitive documents immediately.
One-click revocation (as Firma's engagement Wrap provides) means this is practical for any scenario, not just extreme cases. Standard practice: at engagement end, revoke all client access as part of the close process.
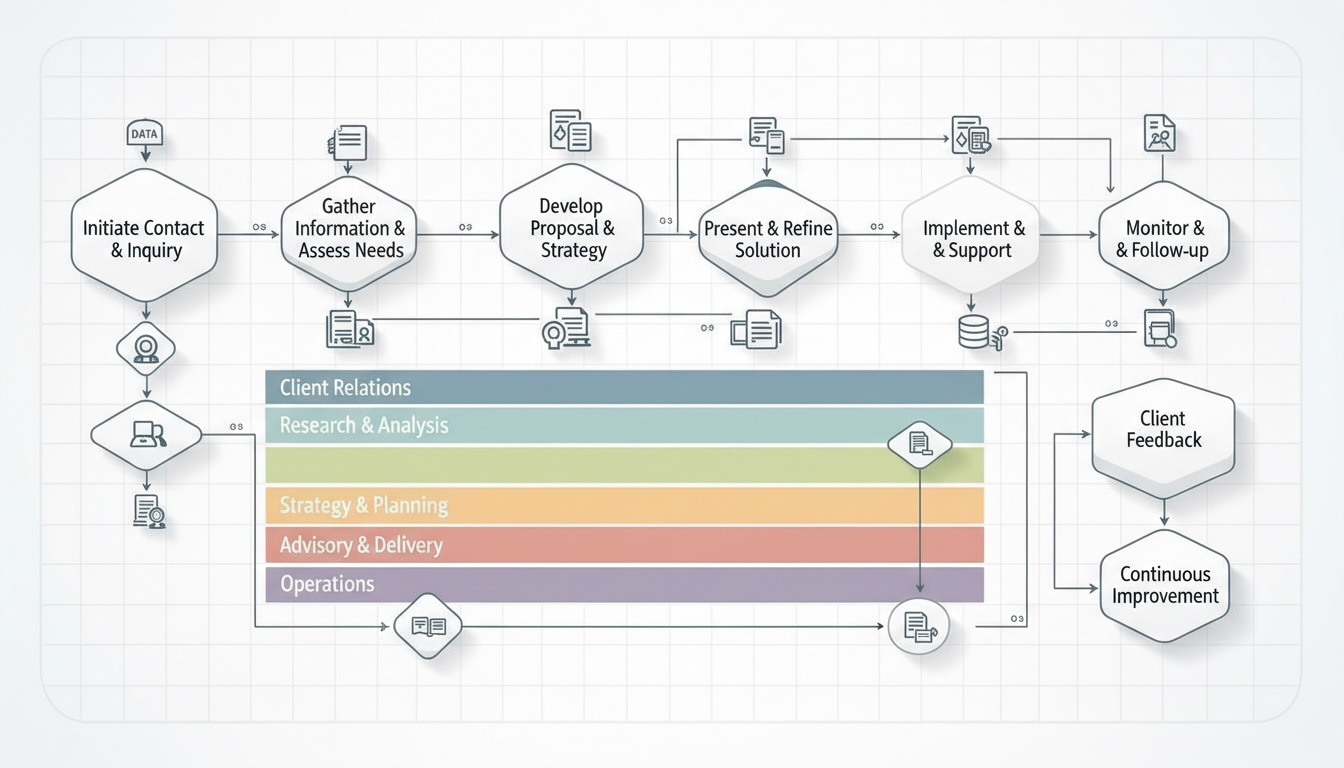
The NDA-Aligned Document Stack
| NDA protection | Technical implementation |
|---|---|
| Prohibits sharing | View-only access (no easy local copy) |
| Time-bounded obligations | Expiring links |
| Evidence of receipt | Access logs |
| Right to request return/destruction | Revocation capability |
| Limited to named parties | Named-user access (not link-only) |
The technical controls operationalise the legal framework. The NDA and the controls work together — the NDA creates the obligation; the controls make it hard to violate casually.
Frequently Asked Questions
What is NDA-proof document sharing for marketing firms?
NDA-proof document sharing combines legal protections (the NDA itself) with technical controls that make casual violations structurally difficult: view-only access (no download capability), time-limited links (self-expiring access), access logging (provable audit trail), and revocation capability (cut off access at any time). Together, these controls align operational security with the protections the NDA is designed to provide.
What are the most important technical controls for sharing confidential marketing documents?
In order of operational impact: (1) view-only access — prevents download and easy forwarding; (2) access logging — creates an audit trail and deters casual sharing; (3) revocation capability — allows immediate access cutoff when circumstances change; (4) expiring links — time-bounds access automatically without manual intervention. These four controls, implemented through a portal like Firma, provide a practical NDA-aligned document security posture.
Does an NDA protect marketing IP without technical controls?
An NDA creates legal recourse if IP is shared in violation of the agreement. Without technical controls, it doesn't prevent sharing — it only establishes that sharing was wrong. For marketing firms sharing genuinely sensitive materials (competitive intelligence, proprietary frameworks, client-specific strategy), legal recourse after the fact is a poor substitute for operational controls that make casual sharing structurally difficult. NDAs and technical controls are complementary, not alternatives.